AI can make software projects faster. At the same time, it introduces risks that traditional development processes do not always cover. Companies that integrate AI into code, support, documentation or business processes without control can create privacy issues, security gaps and decisions that are hard to explain.
The goal is not to avoid AI. The goal is to control AI professionally. Like cloud infrastructure, open source or payment providers, AI needs clear rules, responsibilities and technical safeguards.
The main risk categories
1. Privacy and sensitive information
Many AI risks start with data. Developers paste logs, customer data, database schemas or internal documents into tools without checking whether this is allowed. Even harmless-looking prompts can contain sensitive information.
Companies need clear rules:
- Which data may enter external tools?
- Which data must be anonymized?
- Which systems require local or EU-based processing?
- Who may configure model providers?
- How are prompts and outputs logged?
For sensitive data, a local or private AI architecture can be useful, especially when customer data, contracts or internal knowledge are processed.
2. Hallucinations and wrong assumptions
AI systems can produce plausible but false answers. In software projects, this appears as invented APIs, wrong library versions, incomplete migration steps or architectural suggestions that do not fit the codebase.
Mitigations include:
- explicitly reference sources and files
- require tests for relevant paths
- compare results with documentation
- keep human approval for critical decisions
- never ship unverified outputs
3. Insecure or hard-to-maintain code
AI can create code that works but becomes a long-term problem: broad permissions, weak error handling, duplicated logic, poor typing or unclear ownership.
The review must ask more than "does it run?"
- Does it fit the architecture?
- Are there unnecessary dependencies?
- Are secrets protected?
- Are error states handled?
- Are permission and edge cases tested?
4. Prompt injection and tool misuse
When AI systems read external content or use tools, a new attack model appears. A document, website or user message can contain instructions that try to make the system behave incorrectly.
The OWASP Top 10 for LLM Applications describes these risks as a central category for modern AI applications. For companies, this means AI agents need hard tool boundaries, approvals and filters. A model must not automatically do everything just because a document says so.
5. Missing traceability
If nobody knows which inputs an AI system saw and why a result was produced, operations become difficult. This affects support, compliance and product quality.
A production AI system needs:
- audit logs
- prompt versioning
- model and provider information
- user and permission context
- approval history
- monitoring for errors and drift
Governance: What companies need
AI governance does not have to be bureaucratic. It has to be practical. A good start has five parts.
| Component | Purpose |
|---|---|
| AI policy | Defines allowed tools, data classes and approvals |
| Use-case assessment | Evaluates value, risk and data before implementation |
| Technical guardrails | Roles, permissions, logging, tool boundaries |
| Quality assurance | Tests, evaluation sets, human reviews |
| Operations | Monitoring, error analysis, updates, ownership |
EU AI Act: Not every system has the same risk
The EU AI Act follows a risk-based approach. Not every AI application has the same obligations. An internal code-summary tool must be assessed differently from a system that screens applicants, prepares credit decisions or supports medical recommendations.
Companies should classify early:
- What is the system's purpose?
- Who is affected?
- Are decisions automated?
- Is there human approval?
- Which data is processed?
- Can an error harm people legally, financially or medically?
These questions belong at the start, not shortly before launch.
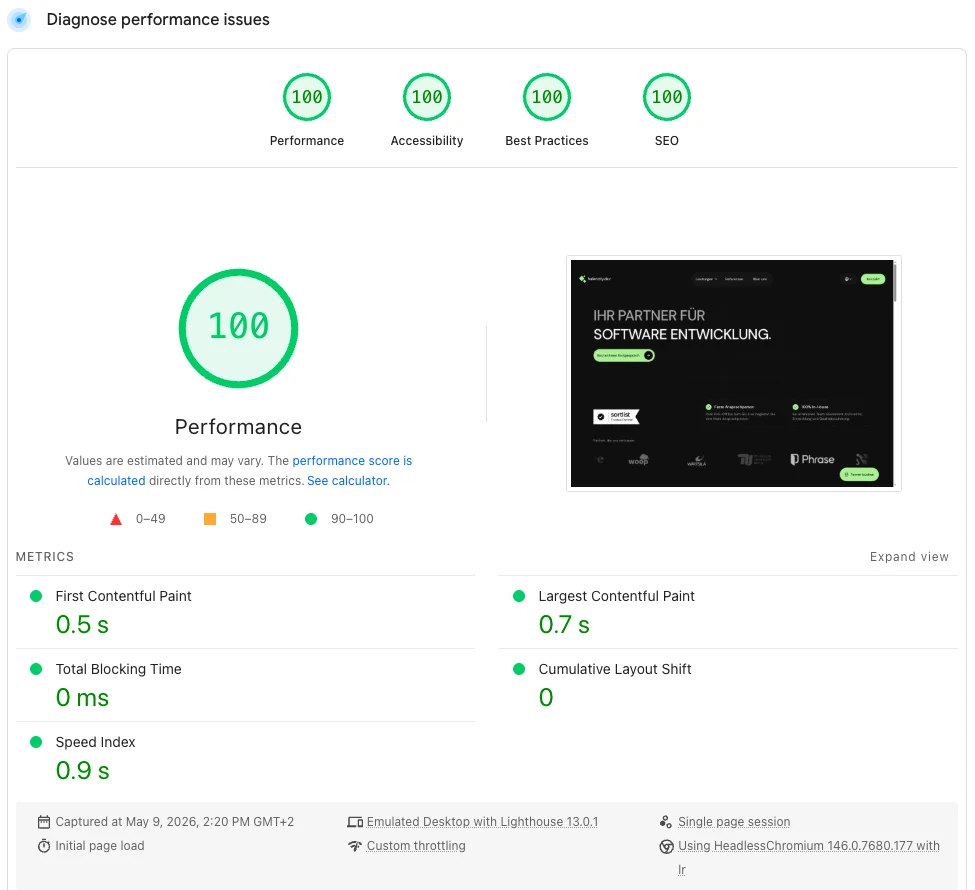
Security architecture for AI projects
A reliable AI integration should be designed like any other production system.
Practical measures include:
- no secrets in prompts
- server-side tool execution with permission checks
- separate development and production environments
- input and output validation
- rate and cost limits
- logging without unnecessary personal data
- approval for irreversible actions
- tests against prompt injection and unauthorized tool use
When local AI makes sense
Local AI or private models are not required for every project. They can be useful when data should not leave the company, low latency matters or industry compliance requires tighter control.
Typical candidates:
- internal knowledge search
- contract and document analysis
- support preparation
- sensitive product data
- research and development
- regulated industries
In these cases, teams should evaluate early whether local models, private deployments or strictly isolated hosting models provide the right technical foundation.
Conclusion: Control risk instead of blocking innovation
AI risks are real. But they are not a reason to avoid AI completely. They are a reason to integrate AI professionally.
At hafencity.dev, we treat AI projects as software projects with special requirements: data flows, permissions, audit logs, tests, evaluation and operations. This creates AI integrations that work in daily use, not only in a demo.